Every year, Statistics Denmark (DST) asks a selected group of Danish companies to submit information about how they use IT, including cloud services and cyber security practices. The exercise is part of an EU wide statistical programme, and it is submitted through Virk, Denmark’s official government self service portal for businesses.
In this article…
- Summary for busy readers
- Why this matters beyond reporting
- What the survey typically asks about
- The quiet shift: governance is now part of cyber security
- What you need to be able to document quickly
- A practical readiness playbook for CISOs and IT managers
- Why the access layer determines confidence
- Where access management supports governance
- Turning reporting into a routine task
For many organisations, the survey is straightforward to complete. The challenge is not the form itself, but having reliable documentation to support the answers.
That is why this type of reporting is worth paying attention to beyond Denmark. Across Europe, cyber security expectations are shifting. The baseline is moving from best practice to demonstrable governance. Organisations are increasingly expected to show oversight, ownership, and supplier accountability, particularly where cloud and access are involved. One clear example is NIS2, which expands requirements and strengthens supervision and enforcement across the EU.
Seen in that context, the ICT survey becomes a useful yearly reality check: can you describe your IT landscape, cloud dependencies, and access controls clearly and consistently.
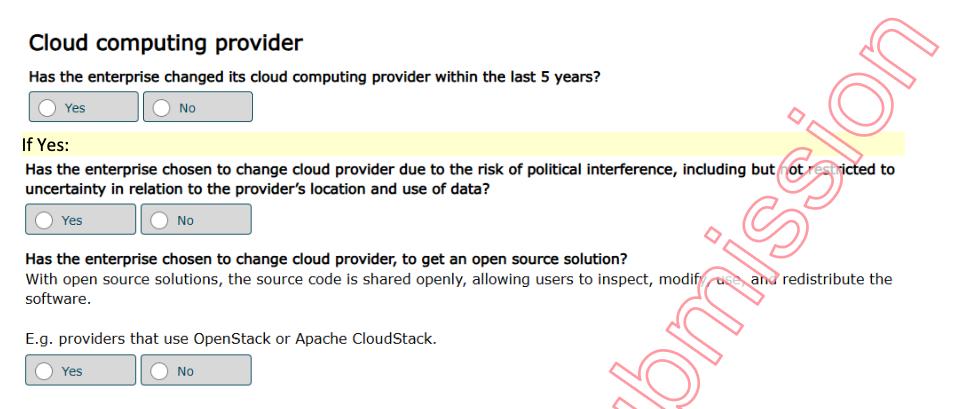
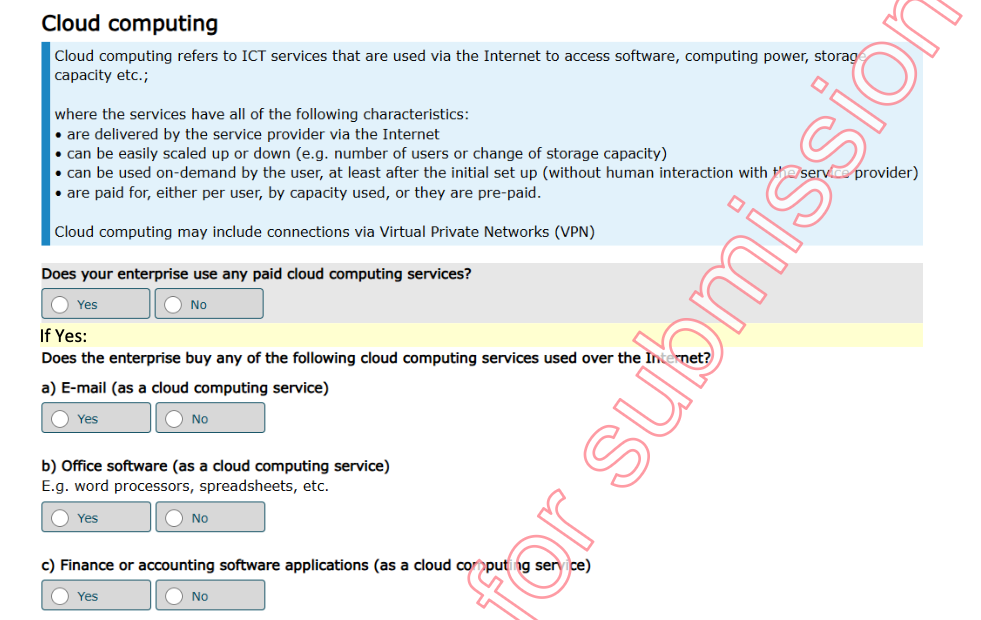
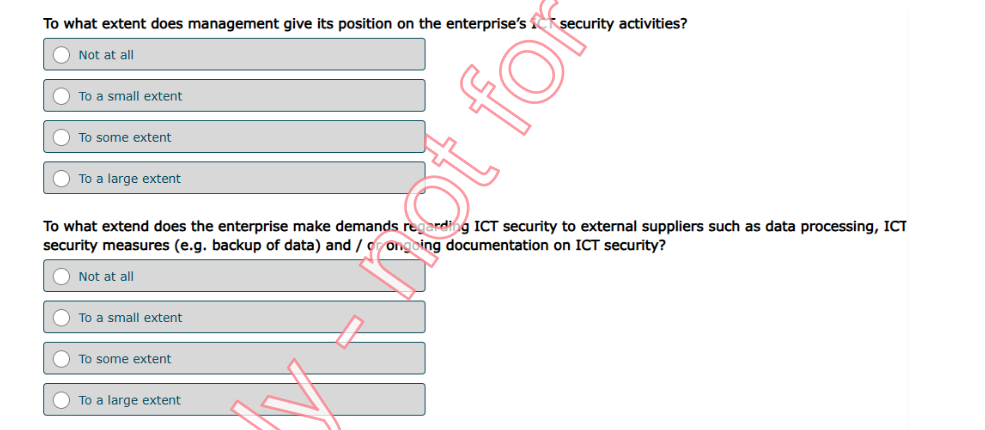
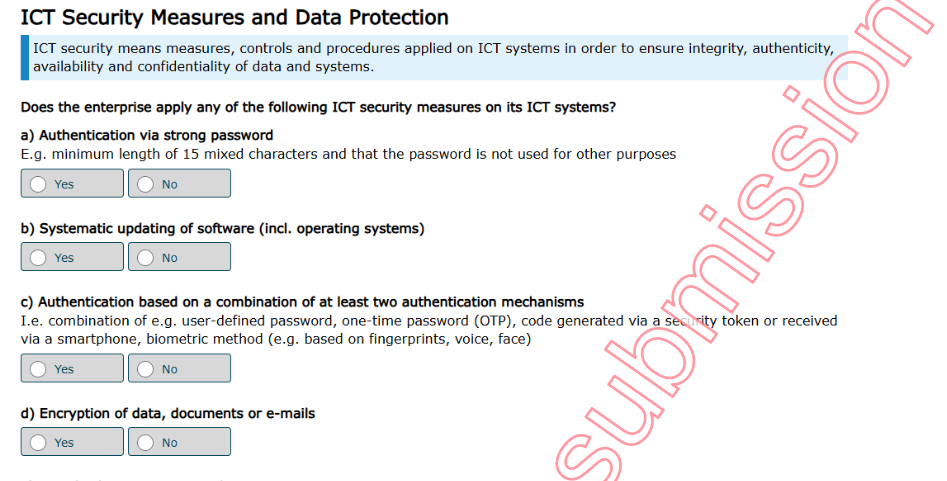
Note: The screenshots below are examples from a draft questionnaire. The exact questions shown in Virk can vary by organisation and by answers.
Summary for busy readers
- The survey itself is rarely the hard part. The hard part is whether you can support your answers with current documentation.
- Across Europe, governance expectations are rising. You need clearer ownership of systems, access, and suppliers.
- Being able to explain what you use, who has access, and how you manage cloud dependencies is becoming table stakes.
- The fastest way to prepare is to maintain a simple access landscape, standardise onboarding and offboarding, and document non SSO coverage.
- A lightweight supplier factsheet for critical vendors reduces effort across reporting, audits, and incident response.
Why this matters beyond reporting
Even though the survey is designed for statistics, it reflects a broader European direction of travel.
The same questions appear in board discussions, supplier reviews, audits, and incident response planning. If you can answer them quickly and confidently, your governance is likely in good shape. If you cannot, the survey tends to expose where visibility and control are missing.
This is not unique to Denmark. The pattern is visible across sectors and countries. In financial services, DORA sets clear expectations around ICT risk management and operational resilience. In cloud markets, the EU Data Act reinforces a growing focus on dependency, portability, and the ability to switch providers. Different instruments, different scopes. The direction is consistent: European organisations are expected to know what they use, who has access, which suppliers matter, and how they maintain control over time.
What the survey typically asks about
The survey covers several themes that cut across IT operations and security.
- IT usage and connectivity
- Cloud usage and dependencies
- Cyber security practices and ownership
- Supplier and third party requirements
- Digital operations and technology adoption
The details vary by year, but the underlying requirement is stable. Your organisation should be able to explain what is used, who owns it, and how it is governed.
The quiet shift: governance is now part of cyber security
Security is no longer only about tools and technical controls. It is increasingly about governance.
- Who approves new systems
- Who can see what is actually in use
- Who reviews access and how often
- Who owns supplier risk
- Who is accountable when access sprawl grows
As organisations rely on more SaaS and more external providers, governance becomes the mechanism that keeps security aligned with reality.
What you need to be able to document quickly
If you want to be ready in the next cycle, focus on your ability to document five areas without last minute reconstruction.
1. Your access landscape
Maintain a current overview of business critical systems and commonly used SaaS tools.
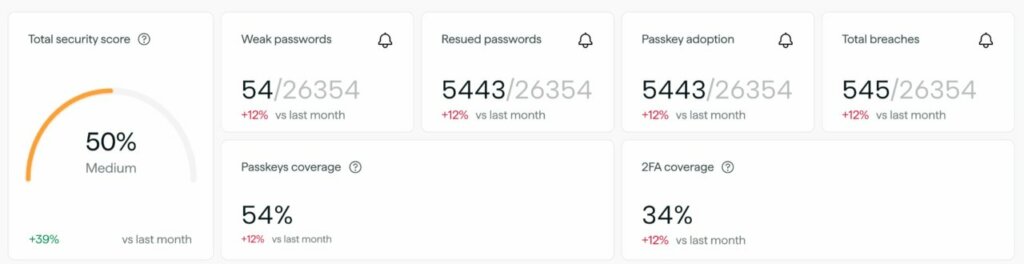
It does not need to be perfect. It needs to be current and owned. Include systems outside SSO, and include tools that departments may adopt independently. The average SMB in Europe uses 185 different services across their organisation, naturally increasing risk and exposing the business to potential threats.
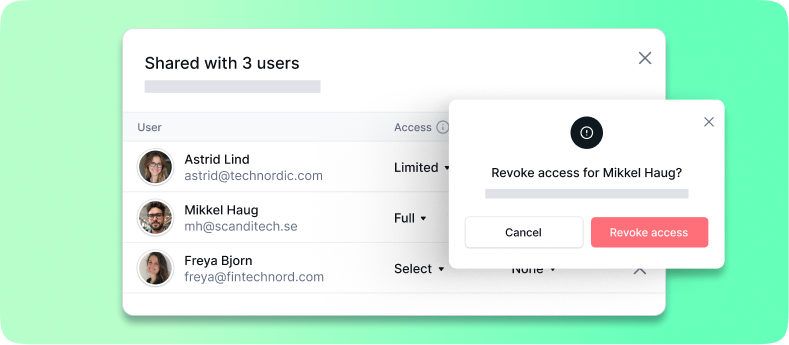
2. Access ownership and lifecycle
For each critical system, document four things.
- Who approves access
- Who can remove access
- How role changes are handled
- How leavers are managed
This is where many organisations struggle, particularly where access is distributed across teams, where external collaborators are involved, or where shared accounts persist.
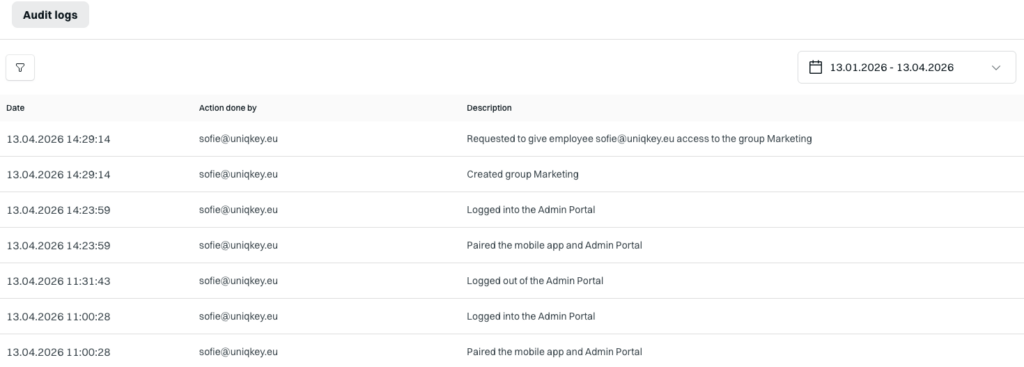
For organisations using Uniqkey, this becomes part of day to day operations rather than a periodic clean up exercise.
3. Authentication coverage and non SSO gaps
Be able to explain where you rely on SSO, where you do not, and how you secure the gaps.
Many teams find that their biggest governance blind spot sits outside SSO. When services cannot be integrated, access control often becomes inconsistent, and documentation becomes difficult to keep current. A password and access management layer that covers both SSO and non SSO services, like Uniqkey, helps close that gap and makes governance easier to demonstrate in practice.
Read more about the SSO security gap in the whitepaper: The SSO Blindspot.
4. Cloud and supplier dependencies
Maintain a lightweight overview of five inputs.
- Which suppliers are business critical
- Where the service is hosted, if known
- Who owns the relationship
- What data categories the service touches
- How you would respond if the service becomes unavailable
This should not be a procurement only exercise. It is operational resilience and security readiness. It is also where expectations are rising across Europe, because supplier dependency is increasingly treated as a resilience issue, not only a contract detail.
5. Evidence you can reuse
Keep relevant documentation accessible and consistent.
- Access policies
- Offboarding procedure
- Supplier security requirements
- High level security reporting
When evidence lives in people’s heads, each reporting cycle becomes a new project.
A practical readiness playbook for CISOs and IT managers
If you want the next request to stay straightforward, treat readiness as an operational habit.
Step 1. Assign one coordinator
One named owner coordinates inputs across IT, security, procurement, and operations. They do not need to know everything, but they need to know where the truth lives.
Step 2. Keep an access map for core systems
Maintain an always current view of who has access to what for your core systems. This reduces reporting effort and reduces real breach risk.
Step 3. Standardise onboarding and offboarding
Access governance fails most visibly at the lifecycle edges: onboarding, role changes, and offboarding. If those processes are consistent, reporting becomes easier and risk drops. 44% of organizations report that new employees are granted excessive access rights during onboarding, increasing the risk of internal security breaches.
Step 4. Document your non SSO coverage
List the systems outside SSO and define how credentials and MFA are handled. These services often have the weakest governance simply because they are harder to centralise.
Step 5. Create a one page supplier factsheet for critical vendors
For each critical vendor, keep:
- Service name and owner
- Escalation contact
- Hosting location, if known
- Whether it is operationally critical
- Whether it holds sensitive data
This supports reporting, audits, and incident response.
Why the access layer determines confidence
Many organisations invest in identity and perimeter controls but still struggle with the day to day access reality.
- Employees adopt new tools faster than governance can keep up
- Credentials are reused across services
- Shared accounts remain because they feel convenient
- Offboarding is delayed because ownership is unclear
When documentation is weak, governance becomes slow. When governance is slow, access sprawl grows. That is why access security and visibility are foundational to answering these questions consistently.
Uniqkey supports this by strengthening credential hygiene and creating a clearer access picture across both managed and unmanaged services.
Where access management supports governance
Access management is one of the most practical ways to reduce uncertainty.
When you can secure credentials across both SSO and non SSO services, maintain visibility into who has access to what, and standardise offboarding, you can answer governance and supplier assurance questions with confidence. It also reduces the likelihood that a minor access issue becomes a major incident.
For European organisations, there is also a growing focus on sovereignty and jurisdiction. Knowing where your access layer is hosted and who has legal control over it is becoming part of security decision making, especially for organisations supporting critical services.
Turning reporting into a routine task
The goal is simple: answers that are consistent, supported, and quick to assemble because the underlying information is kept current.
This is where a strong access layer makes a difference. When access is managed consistently across both SSO and non SSO services, and onboarding and offboarding are standardised, governance becomes something you can document at any time, not only when someone asks for it.


