A strong password policy is your business first line of defense. This is particularly true for businesses, where a breach of security could have disastrous implications, potentially leading to substantial financial losses and a loss of trust among customers and stakeholders. At the heart of cybersecurity lies one simple, yet often overlooked, element: the humble password.
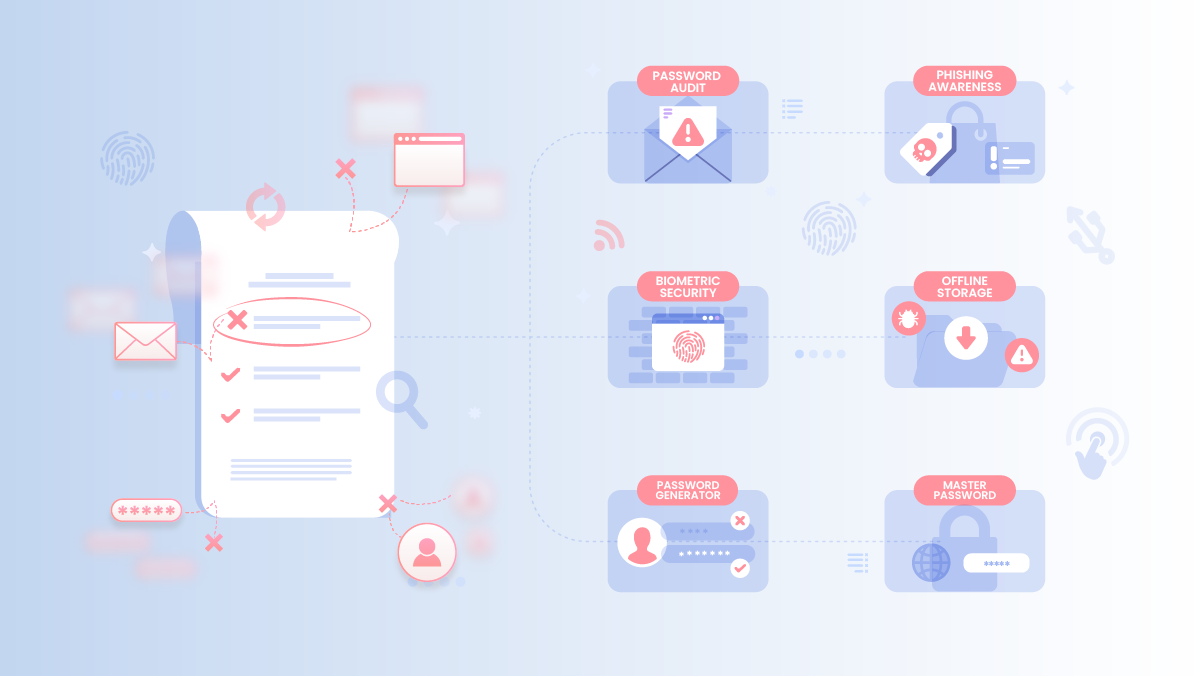
This checklist offers an end-to-end solution, mapping out critical elements of robust password management, including creation, storage, auditing, and employee training. It’s a comprehensive approach to ward off cyber threats, enforce security norms, and instil a culture of cyber vigilance within your organization.
22 Must-Consider Steps for Strengthening Password Security
From password creation and storage to user training and policy enforcement, these measures are a must-consider for any business serious about cybersecurity.
- Establish a comprehensive password policy for the entire organization.
Note: An effective password policy can help to ensure consistent application of password best practices across your organization.
- Ensure all passwords contain a mix of uppercase and lowercase letters, numbers, and special characters.
- Set a minimum password length of at least 12 characters.
Example: Instead of using “secretwordforaccess” consider something similar to “$3cr3tW0rDf0R@cce$$”.
Also Read: The Psychology of Password Creation: Improve Security By Understanding How People Think
- Enforce the use of unique passwords for each account.
- Discourage the reusing or slight alteration of previous passwords.
Note: Hackers often rely on the habit of users reusing passwords or only slightly altering them across multiple platforms.
- Encourage the use of secure password generators to create complex, unique passwords.
Note: Using an advanced Password generators like Uniqkey (built-in) can help avoid human bias in creating passwords and offer a higher degree of randomness and security.
- Use enterprise-grade password management software that can enforce policy, generate audit reports, and automate many of the checklist items above.
Note: Such software can significantly streamline password management and ensure consistent application of policies across the organization. A tool like Uniqkey does exactly this.
- Ensure master passwords are memorable but not easily guessable.
- Discourage sharing of master passwords.
- Encourage periodic changing of master passwords.
Example: A passphrase like “BlueDogsDance@Midnight” is unique but hard to guess.
- Advise treating security questions like passwords, with unique and non-guessable answers.
- Consider using password managers to generate and store answers to security questions.
Example: For a security question asking you for the name of your first pet, you might answer with a randomly generated password stored in your password vault.
- Enable multi-factor authentication on all accounts that support it.
- Encourage the use of hardware tokens for two-factor authentication, if possible.
Note: Multi-factor authentication significantly enhances security by adding an additional layer of verification beyond just the password.
Also Read: What’s The Difference Between 2FA and MFA, And Why Should You Care?
- Implement regular, but not too frequent, password changes.
- In case of a data breach, enforce immediate password changes.
Note: When changing passwords, use a password generator to create a new, strong and completely unique password, rather than simply slightly altering the existing one.
- Encourage storing a physical copy of passwords in a secure location if needed.
- Prohibit storing passwords in plain text on computers.
Note: A password manager like Uniqkey stores your passwords encrypted, offline, and locally on your own device. This is a safer option as there’s no direct connection between your password vault and the internet.
- Emphasize never sharing passwords, even with trusted colleagues.
- If password sharing is required, use secure methods like password manager’s sharing features.
Note: Most password managers let you share your logins in a secure manner and some even allow you to share logins without revealing the actual password.
- Regularly audit passwords for any weaknesses, duplicates, or violations of the password policy.
- Ensure the confidentiality of passwords during audits.
Example: Password managers like LastPass and Uniqkey display how secure your individual passwords are, helping you spot weak ones, so you can take action to strengthen your password security.
- Promote the use of biometric features like fingerprint or facial recognition where available.
- Ensure these features are backed up by strong passwords or PINs.
Note: Biometrics can offer a more user-friendly yet secure method of authentication, but should always be used in conjunction with other measures such as strong passwords.
- Consider using passwordless authentication methods if available and secure, such as biometric access or hardware keys.
Note: Passwordless authentication methods, like hardware keys or biometric authentication, can offer higher security and ease of use but should be deployed carefully and with appropriate backup mechanisms.
- Set up a policy to lock accounts after a specific number of unsuccessful login attempts.
- Have a secure process for unlocking accounts.
Note: This measure can prevent brute-force attacks by limiting the number of failed attempts allowed.
- Maintain a password history to prevent password reuse.
Note: Keeping a password history helps to ensure that old passwords are not recycled, thereby strengthening password security.
- Implement a policy that makes passwords expire at predetermined intervals to ensure regular password changes.
Note: Regularly scheduled password changes can help mitigate the potential damage if a password does get compromised.
- Conduct regular training to make employees aware of phishing attempts.
- Stress the importance of verifying the URL of a website before entering passwords.
Note: Many phishing emails do an excellent job at creating email addresses that at first glance look like a legitimate one. Can you spot the difference between contact@netflix.com and contact@netfIix.com? (The latter one uses a capital “i” to replace the small “L”).
- Have a predefined incident response plan for account breaches.
- This plan should include immediate password changes, contact with service providers, and monitoring for suspicious activity.
Note: Having a plan in place can minimize damage and recovery time in the event of a breach.
- Conduct regular training sessions to educate employees about password-related risks and best practices.
- Teach employees how to spot phishing attempts and other cyber threats.
Note: Regular training can help to ensure that all employees are up-to-date with the latest threats and know how to handle them.
- The IT department should be actively involved in maintaining and enforcing password policies.
- Regularly review and update the password policy in light of emerging cyberthreats and advancements in technology.
Note: Regular updates to the policy will ensure it stays relevant and effective against the latest threats.
- Require managerial approval for certain critical actions, such as overriding password requirements, account unlocks, and policy exceptions.
Note: This adds an additional layer of security and oversight for critical actions.
In conclusion, this password checklist is your holistic toolkit to fortify your digital defense and minimize the risk of security breaches.
It’s not a static document but a dynamic guideline that requires constant updates in response to evolving cyber threats and tech advancements.
By adhering to these principles, your organization strengthens its cybersecurity posture, safeguarding its digital assets and reputation in the process. In the realm of cybersecurity, your password policy is no trivial matter – it’s a critical bulwark against potential cyber intrusions.