A biometric profile is one of the three factors that can be used to authenticate a person’s identity. In multi-factor authentication, a text-based password represents knowledge (something you know), a device or key represents possession (something you have), and biometrics manifest inherence or something you are.
Biometric systems recognize a person’s specific physical attributes – unique features that can be treated as biometric passwords.
Biometric authentication can take various forms like fingerprint scanning, facial ID, Vein/hand scanning, and iris scanning, among others. The most widely used biometric authenticators are fingerprints and facial IDs.
Understanding the biometric authentication process
Biometric authentication is divided into a few simple steps.
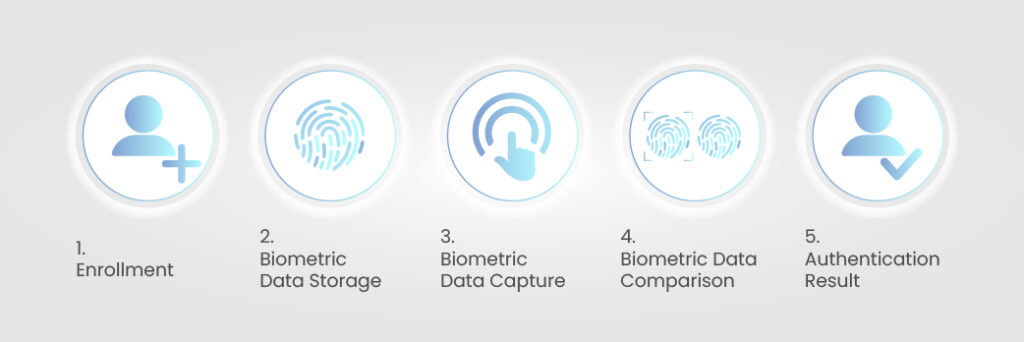
Step 1: Enrollment
Before using biometric data to authenticate an individual’s identity, the biometric system has to collect their biometric data and associate it with their specific identity. For instance, if an individual tries to set up their fingerprint as a biometric password to unlock their smartphone, they’ll need to press the finger several times on the sensor so that the sensor can collect the data.
Step 2: Biometric Data Storage
Once biometric data is collected using fingerprint scanners, iris scanners, or facial recognition systems, it is processed and converted into a code. It can be called a form of encryption since the actual face or fingerprint is not stored and it is not possible to reproduce the face or the finger behind the code.
Step 3: Biometric data capture
When the user attempts to unlock their biometric password-protected device or access a service that requires biometric authentication, they will need to press their finger on a scanner or look into a camera to confirm facial ID.
This can be done through a computer, smartphone, or other biometric-enabled devices.
Step 4: Biometric Data Comparison
Once the user provides the required biometric information, it is codified and the code is compared with the codified biometric data stored in the database.
Step 5: Authentication Result
If there is a close enough match for the captured data in the database, the individual is granted access or denied access.
While the exact steps may vary based on the systems, the above steps present a general idea. Different types of biometric data are captured and stored differently, and the processes may vary based on the kind of data used.
How are different types of biometric data captured?
Each type of biometric information can be captured and stored in many different ways. The following section will discuss some of the more popular methods of capturing and collecting fingerprints, facial IDs, and hand scans.
Fingerprints
The curved lines seen on a human fingertip are called ridges, and the gaps between two ridges are called valleys. The ridges terminate (come to an end) or bifurcate (split in two) in certain locations. These termination or bifurcation points are called minutiae.
The location of the minutiae, the distance between to minutiae, and their distribution patterns are unique for each individual. Information related to the minutiae is mathematically analyzed through algorithms to create numeric codes. There are a few popular methods of capturing the fingerprint data.
Optical Scanner
When an individual places their finger on an optical scanner, it shines bright and takes a digital photograph of the finger. The image is analyzed by a computer using a pattern matching software, and the fingerprint is turned into a code.
Capacitive Scanner
When a finger is placed on a scanner, the finger’s ridges are slightly closer to the sensor’s surface than the hollows between the ridges or valleys. The capacitive scanner electrically measures these distances to create a digital image of a user’s fingertip.
Ultrasonic Scanner
Ultrasonic scanners use high-frequency sound waves or ultrasound to create an image of a fingertip. This process can measure fingertips in three dimensions. While it is slower than capacitive scanning, ultrasonic scanning is supposed to be more secure.
Facial Recognition
Face recognition works by identifying specific features of an individual’s face or its image or video. For instance, every time a person uploads a picture on a site like Facebook, a facial recognition engine is triggered into action to identify the faces in it. It does that by comparing salient features of the faces in the newly uploaded picture with the faces already stored in its database. Similar technology is used in facial recognition for biometric authentication.
The process of face recognition is a bit more complicated than fingerprints. We can go through a couple of methods used for it.
Face Detection using the Viola-Jones algorithm
First, the features of a face are hard-coded into the system. Then a large number of faces was taken as training data. After that, an SVM classifier (support vector machine) is trained on the feature sets. This classifier can later be used to recognize faces.
Face recognition through holistic matching
In this method, Eigenfaces are extracted from images of faces. These Eigenfaces are produced by extracting and normalizing characteristic features of faces. Each Eigenface is represented as a weight of vectors. When the system accepts an unknown image, its weight is compared to that of the weights already stored. If there is a match, the face is recognized.
There are also feature-based, model-based, and hybrid approaches to facial recognition. Facial recognition technology is constantly improving by exploring the advancements made in computer vision.
Vein recognition/Vascular biometrics
This technology is used to measure a subject’s circulatory system. Circulatory systems or the distribution of veins, the distances between them, are unique to each individual. Vascular biometrics explores this uniqueness to create a virtually unspoofable authentication process.
When an individual places their hand on a vein scanner, infrared light is passed through it. The deoxygenated haemoglobin in venous blood shows high red light absorption and low infrared light absorption. This allows computers to create a digital image of the vein structure. The data related to it is used as a biometric signature.
Behavioural biometrics
This discussion has been limited to physical biometrics so far. In fact, most of the biometric authentication systems implemented across industries are based on physical attributes like fingerprints, retina patterns, and facial features. However, there are major strides being made in the field of behavioural biometrics.
In the purview of behavioural biometrics, a person’s gait, keystrokes, lips movement, mouse movement, screen pressure, etc., can be used as biometric passwords. Behavioural biometrics can become a more convenient alternative to physical biometrics because
- The amount of behavioural data and parameters that can be explored is virtually infinite.
- Authentication through behavioural data can be implemented without involving the user.
- It is challenging to determine hence spoof behavioural data.
The advantages of Biometric authentication
1. Increased Security
The uniqueness of biometric data adds security to the authentication method. It is significantly harder for a bad actor to steal biometric data than to steal Passwords or Pins.
2. Convenience and User Experience
Biometric authentication eliminates the need for users to create and remember complex passwords. Not only does this increase efficiency, but it also reduces the risk of falling prey to phishing attacks.
3. Non-Transferable and Difficult to Spoof
Biometric authentication requires the presence of the authorized user. Thanks to the presence of liveness detectors, it is much harder now to spoof biometric authenticators by using images of users
4. Efficiency and scalability
Since biometric authentication doesn’t require tokens or devices for each individual, it is easier to implement for large user bases.
5. Increased accountability
Biometric authentication logs can be easily associated with an individual’s transactions and activities. It increases accountability and traceability in case of a security incident.
Biometric passwords do not ensure absolute security
While biometric passwords are generally considered to be more effective than passwords, as one cannot lose or share them. But they are not absolutely immune to attacks. The following are a few common attacks that can be mounted to cheat biometric authentication.
Presentation attacks
A bad actor can pretend to be someone else by imitating their physical features. Sometimes, biometric authentication systems can be spoofed by such imitations. It can involve holding a high-resolution picture of the genuine user in front of the sensor or wearing meticulously designed masks.
In 2014, a German hacker, Jan Krissler, used a few photographs, including a press photo, to reverse engineer the fingerprints of the then-German minister of defence, Ursula von der Leyen.
Replay attacks
It occurs when a hacker steals an individual’s biometric data in template form as it is transmitted through a network. The hacker can then use the stolen data to impersonate the genuine user and get unauthorized access.
Common disadvantages of biometric authentication
We have already discussed the possibility of attacks against biometric passwords. Even if such attacks are thwarted by particular liveness detector enable systems, other issues challenge the absoluteness of biometric security.
It’s unchangeable
Even if a user’s biometric data is compromised, they cannot change it. In fact, it somewhat resembles using the same password for every account without ever resetting them. This has always been a significant argument against biometric authentication. Nevertheless, the concept of cancellable biometrics is being actively explored by scientists to redress this issue.
False positives/negatives
Unlike passwords or pins, biometric authentication features a level of fault tolerance. The data captured by biometric sensors can vary based on the conditions in which they are captured. The slightest variation in captured data reflects in the numeric information or code associated with it.
The systems are programmed to look for a certain level of likeness between the stored and the captured codes. Hence, it has a range of acceptable inputs and leaves room for both false positives (where unauthorized actors are granted access) and false negatives (where authorized users are denied access).
These disadvantages establish that biometric authentication is not ready to replace password-based authentication. Instead, it can be used as an excellent additional factor in password security.
Biometrics in multifactor authentication
Multifactor authentication and some two-factor authentication systems use biometric information to authenticate an individual’s identity. While biometric data can be insufficient in its security, if used by itself, combined with a strong password, it can become incredibly strong.
Cybersecurity is a vast discipline, and many factors contribute to an organization’s security posture. However, companies that use a dedicated business password manager with biometric authentication are virtually impenetrable when it comes to password security. These password managers create, encrypt, store, and periodically reset passwords, making it extremely difficult for attackers to gain access to accounts.
Additionally, the auditability features of these password managers allow organizations to track and monitor password usage, which can help to identify and mitigate security risks.
To learn more about how to improve your password security, please visit our blog post: Advanced Password Management Techniques: The Pillars of Password Security.
3 Frequently Asked Questions about Biometrics
Which is safer: Biometrics or Text-based Passwords?
Biometrics are safer than text-based passwords on their own, at least from a simplistic, high-level point of view.
In real-time use cases, a number of factors other than the passwords themselves weigh in to determine the level of security, including but not limited to the quality of encryption, the database architecture, and something as simple as the length of a text-based password.
Can biometrics replace password authentication?
No, biometrics cannot replace password authentication because devices and systems will have to depend on passwords or patterns as a fallback mechanism when the biometric authentication system falters.
Can biometric passwords be hacked?
Yes. Almost all kinds of biometric passwords can be stolen, hacked, or manipulated.
Presentation attacks and replay attacks have been used to hack biometric authentication systems for years. Now, digital injection attacks are used to spoof motion and liveliness detectors. In fact, digital injection face swap attacks increased by 295% between the first half and the second half of 2022.