Back in 2015, Cisco conducted a survey in consultation with CIOs from a large number of enterprises across industries on rogue IT systems and unapproved cloud services.
The report indicated that the average number of cloud-based services sanctioned by IT departments was 39. The CIOs’ estimated the number of cloud services or SaaS applications in use within their organizations to be 51 on average.
Marking an astonishing disparity between approval, assumption, and reality, the average number of services actually used by organizations was 730 – 14 times what CIOs estimated and 18 times what IT departments approved.
Consumer-grade cloud services have proliferated since 2015. Many business owners and tech leaders have made the executive decision to leverage shadow IT to some extent, notwithstanding the security risks. The adoption of shadow IT as a viable resource has benefits, provided such resources are brought under adequate governance.
This article will discuss the role that IT governance has to play in the management, moderation, and necessary elimination of shadow IT resources.
Read more on How to detect shadow IT in an organization.
A Brief Introduction To IT Governance
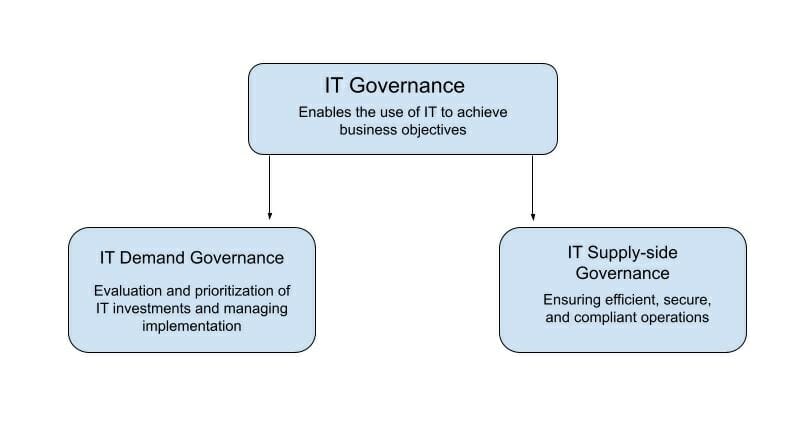
IT governance or ITG is the process that ensures the efficient and effective use of information systems and the technology related to them in enabling an organization to achieve its short-term as well as long-term goals (source) while also ensuring the protection of the organization, its data, and its people.
IT Governance has two main branches.
- IT demand governance ensures that IT investments are tied to business objectives.
- IT supply-side governance ensures that IT resources are utilized efficiently and securely.
The two main branches of IT governance can be divided into five domains
The 5 Typical Domains of IT Governance
- Value delivery: Inspects if the IT-related investments and activities create value for the rest of the business.
- Strategic alignment: Ensures that IT and business goals are aligned and that the alignment is methodically tested and analyzed.
- Performance Management: It inspects how the performance of the IT department is managed.
- Resource Management: Oversees the management of IT resources. Makes sure that the IT resources are utilized effectively, efficiently, and securely.
- Risk Management: Analyzes if risks are duly identified, reported, and mitigated.
Important IT Governance frameworks
IT government frameworks are simply a collection of methods and standards that determine the way IT is addressed in a specific corporate context. The following are some widely used frameworks.
COBIT: Control Objectives for Information and Related Technologies
COBIT helps set up IT control processes that are closely attached to business objectives.
FAIR: Factor Analysis of Information Risk
FAIR is used to quantify the level of risk.
ITIL: Information Technology Infrastructure Library
ITIL helps in the management of IT service life cycles.
CMMI: Capability Maturity Model Integration
CMMI is for effectively developing behavior that reduces risk in service, product, and software development.
An Example of An IT Governance Structure Based On The ITIL Framework
The following table shows how roles and responsibilities are divided within an IT governance structure. This is, of course, a baseline model guided by the ITIL framework. The structure may need modifications based on specific business use cases.
| Roles | Responsibility |
|---|---|
| Governance structure | Responsibilities in organizational governance |
| Board of Directors | – Review IT operations, proposals, and projects – Advise the CIO on matters of demand management, and strategic alignment – Oversee value delivery and risk management – Report to shareholders. |
| Shareholders | – Appoint the board of directors – Appoint auditors – Inspect the quality of IT governance. |
| Audit Committee | – Appoint the board of directors – Appoint auditors – Inspect the quality of IT governance. |
Key objectives of IT governance
- Discovering, mitigating, and eliminating IT-related risk
- Providing proactive IT support toward achieving organizational goals
- Aligning IT projects with business objectives
- Allocating resources and streamlining processes
- Ensuring compliance with security regulations
Understanding Shadow IT as an IT Governance Issue
Shadow IT refers to hardware units and software appliances used within an organization without the knowledge or approval of the IT department. So, by definition, shadow IT obstructs some of the key objectives of IT governance. Also, it stands as a reaction to the failure of IT governance.
For instance, it is one of the objectives of IT governance to ensure proactive IT support toward the fulfilment of organizational objectives. In today’s agile environment, that means empowering teams with the best tools for their day-to-day business activities. The failure to do that results in unsanctioned cloud adoption and employees using an invisible SaaS stack.
It is a vicious cycle where the failure of IT in one aspect leads to the prevalence of shadow IT, which in turn triggers the failure of another aspect of IT governance – security and privacy of data and systems.
If organizations are to operate securely without sacrificing the agility, flexibility, and speed afforded by the adoption of shadow IT solutions by teams, individuals, and in some cases, leaders, IT governance has to step up.
The Action Plan For How To Better Manage Shadow IT:
It always boils down to the same thing: if you don’t allow people to create things in the tools you want them to use, or if you put too much friction between them and getting that done, they’ll go use other solutions.
Marc Anderson
First, the business and IT leaders have to accept the probability of the existence and active utilization of unapproved hardware and software within their organization and address the issue without stigma. The most important step in tackling shadow IT is finding it.
Discovery of IT resources
It should not be challenging for an IT team to deploy a network monitoring system to identify all devices and software appliances running on a network. The network monitoring tool can create an inventory of all connected units and the IT department can identify the unsanctioned teams.
Cloud-based applications used to be a lot harder to trace, but now, many tools are designed to do that. A shadow IT monitoring platform can automate the task of identifying cloud services active in an organization.
For instance, Uniqkey offers CIOs, CISOs, and security admins an interactive dashboard that shows what cloud-based services are active, who is using them, and how frequently they are logging into their SaaS accounts, along with an activity log.

Risk analysis and vulnerability assessment
Once the IT department gains visibility of the unsanctioned assets. It is time to analyze what sort of vulnerabilities that might have exposed the organization to.
Uniqkey’s shadow IT monitoring system assigns a risk score to every software application in the inventory. The risk score can immediately help with the initial filtration of the most risky applications.
From there, an organization can choose to enlist the services of security experts and automated third-party vulnerability assessment tools to dig deeper. This process should help the IT department to reach a shorter list of reasonably secure shadow IT resources.
Identifying and integrating resources that can benefit the organization
Likely, teams have independently found tools that can significantly benefit their productivity, tools that the IT department had failed to provide them with. The IT governance policy should be accommodating of such new ideas.
Reasonably secure tools that employees find beneficial to their work should be duly vetted brought under standard IT protocols, and invested in if necessary. Being able to do that is one of the basic objectives of IT governance.
Establishing channels of communication
The existence of shadow IT indicates the lack of communication between the IT department and the rest of the business. If there are easily accessible channels of communication whereby individuals and groups can inform the IT personnel about their desire to use a specific type of tool to a certain end, the IT department can
- Vet the tool, secure it, and make it visible.
- Direct them to a more secure, maybe already licensed tool that can do the same job.
This is, of course, an ideal case scenario. Issues like lack of IT resources, budget constraints, and even differences in time zones of the employees can obstruct or complicate these processes. Despite the potential hurdles, efforts must be made to establish transparent communication. In the long run, it will help the IT leadership buy more useful licenses.
Create awareness and celebrate innovation
The IT department makes up 6% of a company’s headcount on average. Restricting innovation in IT just to the IT department means rejecting the ideas coming out of 94% of the company. Not only does it deprive the organization of many potentially good ideas, but it also affects the workforce’s morale.
Employees need to be made aware of the risks of shadow IT. Do not tell them that they cannot use anything that the IT department hasn’t approved; instead, encourage them to reach out to the IT department with their ideas, maybe even reward them for finding tools that can really enhance productivity.
Laying down guidelines for data usage and storage
Data privacy and security regulations have never been so stringent. Shadow IT can really disrupt an organization’s compliance with relevant standards, thus incurring fines, penalties, or even legal action. Handling sensitive data is something that the IT department has to control with strict governance policies.
While using a new kind of tool to create a mind map for a marketing campaign might not be harmful, using an unsanctioned, ill-secured cloud storage service to store sensitive data can devastate a business.
IT governance is responsible for drawing the lines when it comes to allowing business-led IT. Every member of every team should be aware of the protocols involving sensitive data, and IT leaders should ensure that these protocols are taken seriously.
Wrapping Up
While members of the IT department may have an excellent understanding of due diligence and secure practices prior to and during the deployment of a solution, they might not have adequate knowledge of the problem other teams are trying to address by adopting shadow IT.
The role of IT governance is to combine knowledge of a problem with the maturity of a solution. Only then can IT departments sanction tools that actually help other teams enough to obviate the need for shadow IT.


