There is little doubt that ensuring organizations are protecting their sensitive data is essential. One of the strongest lines of defence is a solid password policy. Within network infrastructures like Azure Active Directory, these requirements are typically managed under a group policy that dictates password complexity, length, expiration, and other vital parameters.
These policies can be configured through the security settings in the Group Policy Management Console, allowing administrators to manage password requirements and establish account policies to enhance security.
With cyberattacks on the rise, several organizations have turned to best practice recommendations that cover things like maximum password age, minimum password length, domain password policy, and how to correctly store passwords. So, let’s go through the best guidelines to guarantee the strongest possible security in Active Directory.
🏆Uniqkey streamlines password management for businesses with Active Directory, ranked as the easiest to use by G2 and listed among the top 50 global security products. Try Uniqkey for free, Europe’s preferred password security platform.
What is a Password Policy, and Why Does It Matter?
Simply put, a password policy is a set of rules and requirements to do with the creation, usage, and management of passwords. In other words, these guidelines outline the different standards that users should follow when setting their passwords for various systems.
A compromised user account can lead to network breaches, making it crucial to have a strong password policy to protect against such vulnerabilities.
The ultimate goal of a password policy is to improve the overall security posture of any digital environment.
How?
By making sure no unauthorized people can access sensitive data. But that’s not all. Fine-grained password policies also contribute to the following:
- Compliance and standards: Many industries have specific regulations and compliance standards, such as GDPR, HIPAA or PCI DSS. All of these require the maintenance of specific and strong security practices. In many cases, a password policy is necessary to adhere to these standards.
- User accountability: Password policies can also help create accountability among a system’s users. These policies set clear expectations for password creation and maintenance and ensure employees understand their responsibility to secure accounts.
- Preventing common attacks: Some of the most common attacks include brute force, dictionary attacks, or phishing attempts – all of which tend to target weak passwords. A password policy that enforces complexity and periodic changes (for example, through maximum or minimum password age) can significantly reduce the success of such attacks.
- System integrity: Lastly, strong passwords contribute to the overall integrity of systems and networks. This makes the system itself more resilient, reducing the potential for downtime or data loss due to unauthorized access.
Creating a reliable password policy, thus, involves specifying things like minimum password length, complexity requirements (including the need for users to include special characters, uppercase/lowercase letters, and numbers), expiration periods, restrictions on password reuse, and account lockout policies after multiple failed attempts.
The Default Domain Password Policy in Active Directory
Within Active Directory, the Default Domain Password Policy is a baseline set of rules and requirements for password management within a Windows domain. This policy sets the minimum security standards for user passwords across the entire domain, so when you install Active Directory on a server, the default policy is automatically applied to it.
The Default Domain Password Policy includes the following elements:
- Password length and complexity: A set of minimum password length and complexity requirements, such as a minimum number of characters, a mix of uppercase and lowercase letters, numbers, and special characters.
- Password history: A history of previously used passwords to prevent users from reusing the same password repeatedly (so users can’t cycle back to previously compromised ones).
- Password expiration: A time limit for the validity of a password and the requirement to change passwords after a defined period.
- Account lockout policy: A specification of the number of failed login attempts permitted before an account gets temporarily locked or disabled (which helps with brute-force attacks).
- Fine-grained password policy: Windows Server editions that support Fine-Grained Password Policies allow admins to customize multiple password policies for specific sets of users or groups within the domain.
Now, while the default password policy provides a foundational level of security, you can (and should) further customize and strengthen your password policies based on both requirements and best practices. So, let’s take a look at those next.
Active Directory and Password Policy Settings Best Practices
As we have covered above, the default domain policy settings will apply to all accounts within a domain. However, admins can also create more specific rules within the Active Directory Management Center (ADAC) in Windows Server. All of these should, however, follow best practices to guarantee safety.
Best Practice #1: Configure a Minimum Password Length
Setting a minimum password length is essential for establishing a baseline security standard. Longer passwords generally increase complexity and make them harder to crack. So, what is a good length? The standard recommended minimum is eight characters, but it’s okay to aim for even longer passwords, such as 12 to 16 characters.
📚Related: Password Checklist: Protect Your Business from Breaches
Best Practice #2: Enforce a Password History
Cyber attackers often exploit human behaviour, such as the tendency to reuse familiar passwords, to gain unauthorized access. Having a solid password history can prevent users from reusing previous passwords – which might already be compromised. User-generated passwords are often weak and predictable, making it essential to enforce a password history to ensure users create new, unique passwords. This prevents users from cycling through a limited set of passwords (which should also not have been used in any other platforms or services), reducing security risks. In other words, when users cannot revert to their previous passwords, they are compelled to create new, unique, and typically more secure passwords.
Best Practice #3: Set a Minimum Password Age
Implementing a minimum password age also helps prevent users from rapidly changing their passwords and revert to a previously used one. One way to easily do this is to establish a waiting period before allowing a password change. Without a minimum password age, users might attempt to bypass the password history check by quickly changing their passwords multiple times. A minimum password age adds a layer of protection against quick password rotations to evade the history check.
Best Practice #4: Always Include Complexity Requirements
A strong password policy should always also enforce complexity requirements. For instance, by mandating a mix of character types (upper and lower case letters, numbers, and special characters). This significantly enhances the strength of passwords, making them more resistant to brute-force and dictionary attacks.
Best Practice #5: Reset Local Admin Passwords Regularly
Local administrator accounts are highly sought after by attackers. If compromised, these accounts could provide unauthorized access to individual devices or segments of the network, leading to potential data breaches or the compromise of critical systems. Regularly changing local admin passwords can reduce the risk of unauthorized access to critical systems. So, this practice should be followed in addition to domain admin passwords to bolster the overall security posture.
Best Practice #6: Use Strong Passphrases for Admin Accounts
Domain admin accounts need to be even more secure than those belonging to users. For one, they should always be at least 15 characters. Passphrases, which are longer combinations of words or phrases, are a good idea to increase security. Thus, encouraging the use of passphrases for admin accounts significantly strengthens protection against brute-force attacks.
Best Practice #7: Track All Password Changes
Maintaining a log of password changes enables administrators to monitor and investigate any suspicious activities. Logging changes can also provide crucial information in the event of a security incident or the need for an audit. So, it’s best to always keep and enforce password history policies.
Best Practice #8: Incorporate Email Reminders
You can send regular reminders to change passwords via email to ensure users are consistently prompted to update their passwords. Sending periodic notifications, whether monthly, quarterly, or based on the organization’s policies, serves as a gentle nudge for users to update their passwords. These reminders should ideally also include best practices and guidelines to help users create secure passwords.
Best Practice #9: Create Granular Password Policies
You can also use Fine-Grained Password Policies to create more specific rules for different groups or individuals within your organization. Different groups within an organization might have varying security requirements. For instance, the finance department may require more stringent password policies compared to other departments due to the sensitivity of financial data. FGPP enables tailored policies to meet these varying needs. This granularity allows tailored security measures to meet different security requirements across various user groups or departments.
Best Practice #10: Educate Users
Lastly, training and educating users on the importance of strong passwords, recognizing phishing attempts, and understanding best practices in password security are crucial. If an attacker compromises a user’s account, it could grant them access to a broader range of sensitive information, highlighting the importance of strong password practices. All of these practices empower users to actively contribute to the security of the system and become the first line of defence against unauthorized access.
Implementing Fine-Grained Password Policies
Fine-grained password policies (FGPPs) offer a powerful way to tailor password requirements to meet the specific needs of different user groups within an organization. Unlike the default domain password policy, which applies universally, FGPPs allow for more nuanced control, ensuring that higher-risk accounts, such as admin accounts, have stricter requirements.
To set up FGPPs, you will need to use the Active Directory Administrative Center (ADAC). Here’s a step-by-step guide:
- Open ADAC: Launch the Active Directory Administrative Center.
- Navigate to the Domain: Click on your domain to access its settings.
- System Folder: Go to the System folder within the domain.
- Password Settings Container: Click on the Password Settings Container.
- Create New PSO: Click on New > Password Settings Object.
- Configure Settings: Enter a name for the password settings object and configure the desired password policy settings, such as minimum password length, complexity requirements, and password history.
- Apply PSO: Once configured, click OK to create the password settings object.
FGPPs can be applied to specific groups or organizational units (OUs), allowing administrators to enforce different password policies for different departments. For example, you might require the finance department to use more complex passwords due to the sensitivity of financial data, while other departments might have slightly less stringent requirements.
By leveraging FGPPs, you can ensure that your password policies are both flexible and robust, providing enhanced security tailored to the unique needs of your organization.
Password Management and Security
Effective password management and security are cornerstones of any robust cybersecurity strategy. A well-defined password policy not only protects user accounts but also safeguards sensitive data from unauthorized access.
Troubleshooting and Maintenance
Maintaining and troubleshooting password policies is essential to ensure they remain effective and relevant. Here are some common issues and how to address them:
An Easier Way to Integrate Active Directory
If you’re looking for an easy way to manage your employee or user’s passwords, we can help.
Uniqkey has direct Integration with Microsoft Active Directory. As an admin, you can sync via SCIM integration and manage all access rights directly from the Uniqkey dashboard! This allows you to see the security of the users or control it.
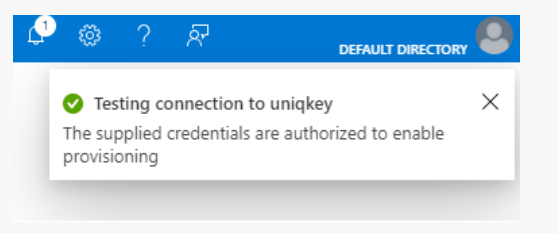
All you need to do is navigate to your Enterprise Applications within your Azure Active Directory and create a new application. From here, you will be able to manage all your users and groups – as well as their policies, all within a single tool. single tool.
💡Offboarding employees can be time-consuming, pose security risks, and lead to wasted funds on unused licenses. For CFOs aiming to control budget waste, this is challenging. However, Uniqkey can streamline this process, ensuring security and financial efficiency.
Uniqkey makes password management simple. Contact us today to discover the full potential of Active Directory with Uniqkey to manage all passwords and security effectively.


