Passwords are not enough to ensure the security of your accounts across various web or app-based services, making robust user authentication essential. 41,970,182 records were compromised in March 2023 in 100 publicly disclosed incidents. These records include personally identifiable information as well as user IDs and passwords.
Even though passwords in a database are encrypted, it’s a matter of time for hackers to decrypt them and turn them into plain text. Hence, your password-protected account needs an extra layer of security: two-factor authentication or 2FA.
In this post, you’ll learn what 2FA is, its types, and how different methods of 2FA perform in terms of security and UX.
2FA is “an authentication system that requires more than one distinct authentication factor for successful authentication.” (source.))
Of the 3 primary authenticators – knowledge, possession, and inherence – 2FA uses the first two i.e. knowledge (something you know), and possession (something you have).
In most cases, the knowledge factor is covered by the user ID and password or the credentials. The possession factor is usually confirmed by a device you possess: a registered mobile device or a USB key.
The inherence factor, which can include biometric identifiers like an individual’s fingerprints, retina patterns, or voice characteristics, is left out of 2FA.
Table of contents
Understanding 2FA
Two-factor authentication (2FA) is a security process that requires a user to provide two different authentication factors to gain access to a system, network, or application. This adds an additional layer of security to the traditional username and password combination, making it more difficult for attackers to gain unauthorized access.
2FA is based on the concept of “something you know, something you have, and something you are.” The three factors are:
- Something you know: This typically involves a password, PIN, or passphrase. It’s the most common form of authentication and is something only the user should know.
- Something you have: This could be a physical token, smart card, or mobile device. For instance, a registered mobile phone can receive a one-time password (OTP) via SMS or an authenticator app.
- Something you are: This involves biometric data, such as fingerprints, facial recognition, or voice recognition. Biometric verification ensures that only the actual user can gain access, adding a robust layer of security.
By requiring two of these factors, 2FA provides a more robust security mechanism than traditional single-factor authentication. This multi-factor authentication (MFA) approach significantly reduces the risk of unauthorized access, as an attacker would need to compromise two separate authentication factors.
How Does 2FA Work?
First, you have to enable 2-factor authentication to verify the user’s identity. If a service provider supports 2FA, you’ll be prompted to enable it. All you need to do is register a phone number, a device, or an email account that can be used to verify your identity.
The service will send a signal to your device whenever you try to log into your 2FA-enabled account with a user ID and password. It can be a prompt asking you to tap yes or an SMS with a one-time password that you have to enter into an input field.
Types of Two-Factor and Biometric Authentication
2FA can take different forms based on the authentication method used. We’ll discuss four modes of authentication. Three of them are commonly found and one is not so common.
Type 1: Time-based One-time password or TOTP with Authenticator Apps
TOTP, or time-based one-time passwords, uses time as one of the authenticating factors. It involves an algorithm that generates rotating passwords with momentary validity. A user trying to log into a service may receive the TOTP via an authenticator app, a hardware security token, or an email or message. Authenticator apps have gained a lot of popularity across industries due to their ease of use on mobile devices.
Type 2: SMS based on Mobile Device
2FA through SMS has a simple flow on the user end. First, you provide the service with your phone number to set up the 2FA. When you type in your login credentials, the service generates an OTP and sends it to your registered phone number via SMS text message. Once you receive the OTP message, you manually enter the OTP to log into your account.
Type 3: Push Notifications
The push notification system uses an authentication server that sends a notification to a device tied to a registered phone number or an email account. The notification itself contains information about the attempted login – the name of the device being used to log in as well as its location. The user is given the choice to approve or disprove the login.
Type 4: U2F or Universal 2nd Factor
U2F involves a piece of hardware – security keys – that are used to authenticate a user’s identity when logging into a specific service. U2F is considered one of the most secure methods of 2-factor authentication. However, it is not the most popular one.
2FA Rankings – Based On Their Security and User Experience
2FA in various forms has been facing rejection since the early 2000s. In 2019, The New York Times reported that Google had gotten only 10% of its users to sign up for 2FA. In 2021, Google made 2FA mandatory and auto-enrolled 150 million users for 2FA by the end of that year. In 2022, the tech giant saw a 50% security boost for all those accounts.
2FA is more secure than the simple password but a little more cumbersome for the users. But all authentication modes are not equally secure, nor are they equally irritating for the users.
If we rank different modes of 2FA based on UX and security, we will get different results. While this is arguable, we can contend that considering security as the only driving factor, types of 2FA stand in the following order:
U2F > TOTP > Push > SMS
If we take user experience as the key factor, the methods stand
Push > SMS > TOTP > U2F
In any case, SMS is the least secure mode of 2FA and we’ll explore why.
What Makes One Form of 2FA Less Secure Than The Other?
While 2-factor authentication adds a layer of security to your password-protected accounts, it doesn’t guarantee absolute immunity against hacking attempts. There are various ways in which hackers may try and get around the 2FA, and some methods of authentication make it harder for them to do so than others.
SMS stands as the least secure mode of 2FA
When you enter your credentials to log into an account the service generates an OTP and sends it to your registered mobile number. The SMS comes via a telecom company. And that is where the problem lies.
Strategies hackers use to steal one-time passwords and access your account
Scenario 1: Phone number porting
A hacker steals your password and gets hold of your telephone number. Now, they convince your phone’s network provider to activate a new sim card for your number. They enter the stolen password into the service, receive the OTP, and get into your account.
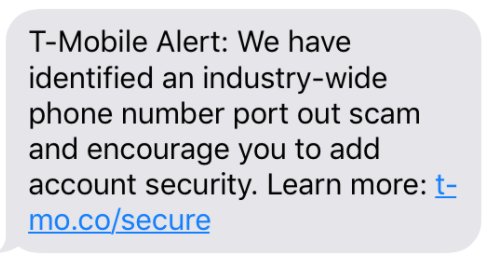
In 2018, T-Mobile sent text messages warning the masses about an industry-wide “phone number port out scam.” The company advised users to find alternatives to text-for-pin authentication.Scenario 2: Phishing
The hacker doesn’t have your password or access to your number but they lure you into a phishing site that is a carbon copy of a service website you want to log into.
- You enter your login credentials into the phishing site
- The hacker steals them and enters into the real site
- The service generates an OTP and sends it to your number
- You manually enter the OTP into the phishing site
- The hacker copies the OTP and enters into the real site.
A 2017 report by Google said, “We find victims of phishing are 400x more likely to be successfully hijacked compared Page 2 to a random Google user”Scenario 3: Redirecting messages through SS7 hack
Hackers can redirect a user’s text by exploiting the inherent vulnerabilities in the signal system 7 or SS7 telecommunication protocol. Thus, messages sent to legitimate users for authentication are redirected to hackers.
In January 2017, hackers used this method to drain bank accounts that were protected by 2FA. Push Notifications Are Relatively Secure But Only If You’re Alert
As we’d mentioned earlier, push notifications come with the device name and the login location.
Let us say, you enter your credentials into a phishing site, and the hacker steals them and enters into the real site. Now, the service will send a push notification to the registered device which is your phone. Before you approve the login, take a moment and check the device name and the location. You should be able to notice that the login request is not coming from your device. Do not approve it.
The Time Factor Makes TOTP More Secure Than SMS
Here is how the Time-based OTP authentication usually flows:
The service provider shows QR on the browser and you use an authenticator app to scan the QR to get the OTP. Then you type the OTP into the browser to log in. The OTP keeps changing periodically.
If you ever lose the device with the authenticator app, you can use the recovery codes to regain access. Recovery codes are provided to you when you first set up the authenticator. You need to keep them in a safe place.
Hackers can use phishing sites to get into accounts protected by TOTP but since the OTPs rotate within a very short time span it is a lot harder for hackers to use them for unauthorized access.
U2F is The Most Secure (But Least Practical) Method of Authentication
The following is how U2F authentication functions
- The user enters the password and then inserts the security key into a USB port
- A key pair is generated and bound to the origin
- The service sends a challenge to the browser
- The browser directs the challenge as well as the origin to the security key
- If the user inserted security key matches with the origin-bound key, the challenge is signed
- The signed challenge goes back to the service via the browser service verifies the signature and lets the user log in.
U2F creates user experience issues as it requires additional hardware. Users often struggle to find a free USB slot to insert the key. There is always a chance of losing the key. If you ever lose the hardware, there is no way of recovering access.
Hence, If we try to strike a balance between user experience and security and rank 2FA methods based on both, we get
TOTP > Push > U2F > SMS
The important thing to notice is that any form of 2FA is more secure than just a password. The deterioration of UX is the main reason why a lot of services struggle to have their users sign up for 2FA.
Three out of four enterprise security managers aim to boost their investment in multi-factor authentication. Solutions like Uniqkey can aid in building a more secure infrastructure at a reduced cost for businesses.Implementing 2FA
Implementing 2FA can be done in various ways, depending on the specific requirements and constraints of the organization. Some common methods include:
- SMS-based 2FA: This method sends a one-time password (OTP) to the user’s mobile device via SMS. It’s a common method but has some security vulnerabilities, as discussed earlier.
- Authenticator app-based 2FA: Using an authenticator app, such as Google Authenticator or Authy, to generate a time-based OTP. These apps are popular because they offer a higher level of security compared to SMS-based methods.
- Biometric-based 2FA: This method uses biometric data, such as fingerprints or facial recognition, to verify the user’s identity. Biometric authentication is highly secure as it relies on unique physical characteristics.
- Hardware token-based 2FA: This involves using a physical token, such as a smart card or USB token, to generate an OTP. While highly secure, it can be less convenient due to the need for additional hardware.
When implementing 2FA, it’s essential to consider the following factors:
- User convenience: 2FA should not be too cumbersome or inconvenient for users. The goal is to enhance security without significantly impacting the user experience.
- Security: The chosen 2FA method should provide a sufficient level of security to protect against unauthorized access. It’s crucial to balance security with usability.
- Cost: Implementing 2FA should be cost-effective and not require significant investment in hardware or software. Organizations should consider the long-term benefits and potential cost savings from preventing security breaches.
- Scalability: The 2FA solution should be able to scale to meet the needs of the organization. As the organization grows, the 2FA system should be able to accommodate an increasing number of users and devices.
By carefully considering these factors, organizations can implement a 2FA solution that enhances security while maintaining a positive user experience.
Recommendation and Bottomline
A solid password manager like Uniqkey helps you log in automatically to online accounts. Not only does it enter your credentials, but it also fetches the 2FA information to make the authentication process completely hassle-free.
Businesses often avoid using two-factor authentication (2FA) because it can cause issues with user experience. Employees are worried about the authentication process reducing their efficiency.
Uniqkey’s auto-fill feature eliminates these concerns. More importantly, since you are not inserting the credentials or the OTP, phishing sites are no longer a threat. To see Uniqkey in action, request a 14-day free trial.


